A proven strategy
Outline your business needs around data protection and information handling with guidance from Fortra's Data Classification Professional Services team. By engaging with stakeholders from across your organization, we can ensure that everyone has an agreed-upon blueprint to follow as your data security solutions roll out to users.
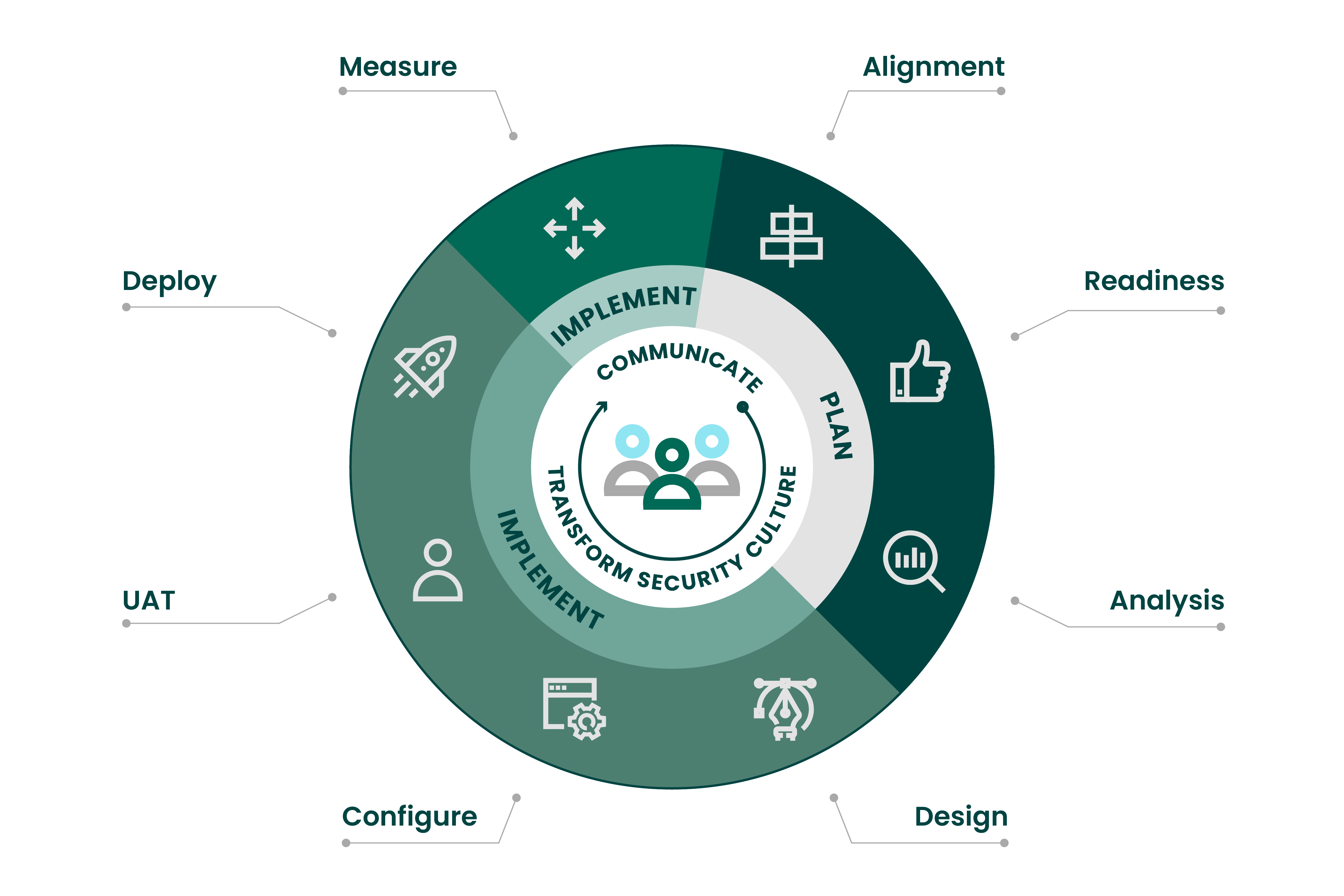
Our deployment process

We follow three phases designed to help you meet these very important goals:
- Educate stakeholders and employees on best practices for handling personal information to create a culture of security within your organization.
- Empower users with the information and tools they need to make suggested classifications based on your organization’s policies.
- Enforce your policies through data handling restrictions and integration with your other data security investments.
Step 1: ENGAGE
Before any technology discussions occur, we engage with you for deep planning. It’s critical to identify your business stakeholders, including account executives, sales engineers, professional services team members, product managers, people from customer service management, human resources, and other departments. All of these people must be involved at every step of the way. As a team, we will review the data classification implementation methodology and align on the functionality your organization needs to implement.
At this initial stage, it’s critical to discuss roles and responsibilities, identifying specific individuals who will approve each step along the way.
- Set up a process for providing feedback during implementation.
- Review key success factors.
- Align on a communications plan and strategy that keeps employees informed — beginning now.
- Map out user acceptance testing (UAT) strategy and identify stakeholders.
- Review requirements from important departments or countries.
- Consider compliance mandates and other external factors.
- Determine whether your existing technologies will leverage the classification metadata for optimization (data loss prevention (DLP), archiving, etc.).
- Identify a long-range vision for classification in the organization (with flexibility in mind).
Step 2: DESIGN
Next, our Professional Services team will work with your IT team to design the architecture for your classification solution, including your schema and governance controls. We will also help establish a policy workflow to meet phased criteria.
- Consolidate input from the Engage step and use it to define labels, policies, and workflow for your technical configuration.
- Evaluate classification label and policy best practices.
- Review labels and policies with stakeholders for approval and sign-off.
- Identify a reporting strategy.
Step 3: CONFIGURE
This phase consists of the technical implementation of your requirements from the design phase. We will work with your tech team to build your configuration within Fortra's data classification administration console. If necessary, we will engage your other security technologies to integrate with data classification and make use of metadata for monitoring or policy implementation.
- Perform testing across user communities.
- Review, adjust, and update your configuration based on feedback.
- Engage technical stakeholders to get sign-off.
Step 4: DEPLOY
At this stage, your business leaders should make an announcement to the organization about the phased rollout to users.
- Identify any feedback that may require a configuration change.
- Provide promotional and training tools such as placemats, badges, and screensavers.
Step 5: MATURE
Once your data classification solution is up and running, you will continue to run reports to monitor the key success factors that were identified during the ENGAGE stage. It’s a process that will continue as your business evolves and you identify new success factors. The reporting functionality allows you to identify the amount of data being classified as well as events that are preventing data leaks. You can also use reporting to identify trends that may require a change to the classification configuration.
- Invite users to new product release webinars.
- Collect feedback to design product enhancements.
- Evaluate holistic needs for classification and information protection.
- Review evolving internal and external drivers for classification (new policies, legislations, regulation, standards, etc.).
Download the DCS Deployment Methodology solution brief
Learn more about our proven implementation strategy and exactly how you can successfully deploy a data classification solution to meet your unique data security needs.
DCS deployment: Implementation timelines
The DCS deployment methodology offers organizations an iterative framework to effectively deploy policies in a manner that ensures a positive user experience and with an eye toward ongoing evolution.
How protected is your data?
Meet with one of our experts to assess your needs, and we'll walk you through our solution.